Security
Some interesting takeaways from this year's Techorama
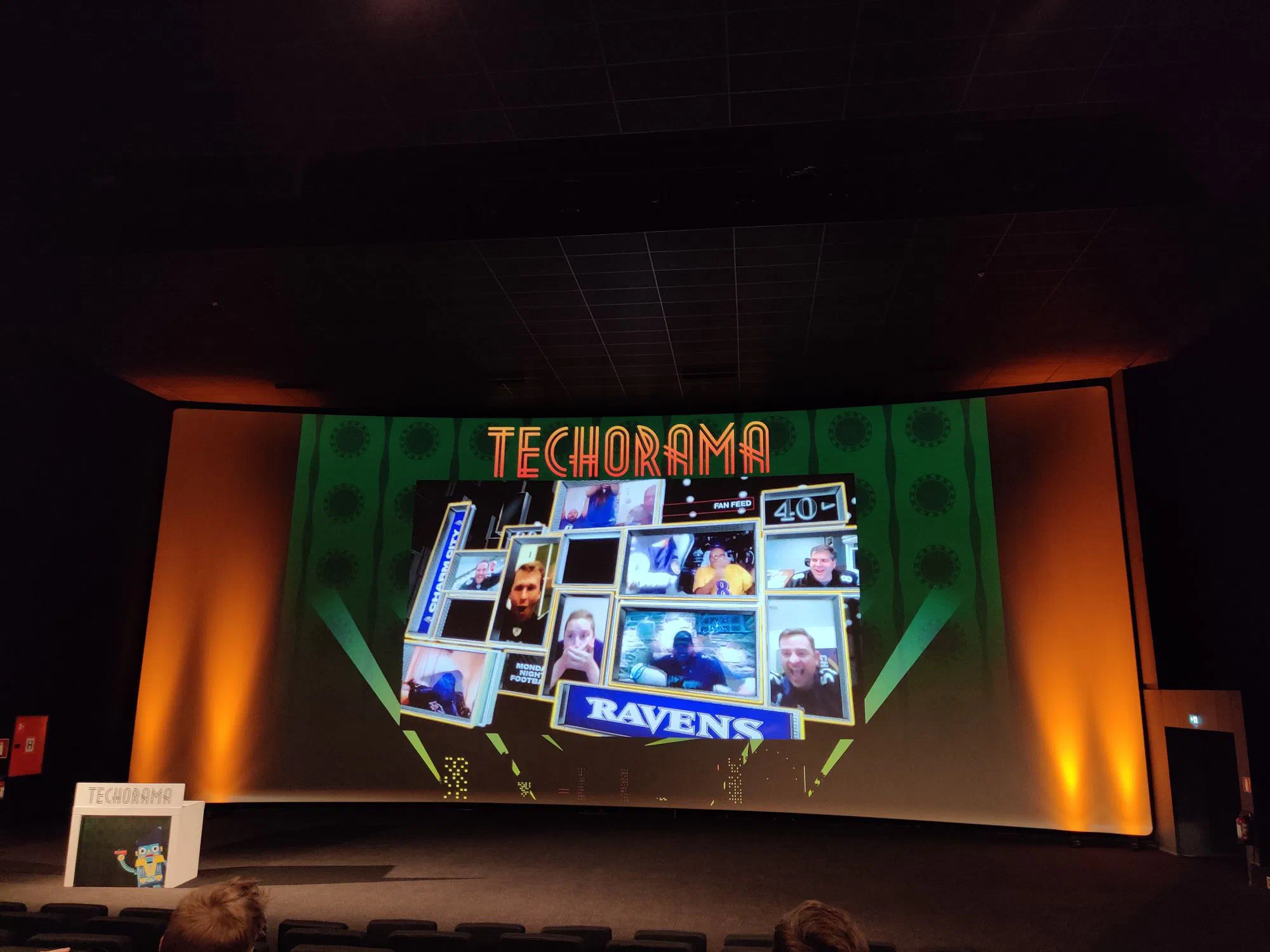
Last week was a busy week for fans of the Microsoft technology stack like myself. Microsoft hosted its yearly developer conference, Microsoft Build, announcing lots of exciting updates to new and existing Azure services. In the meantime, the Belgian community of Microsoft technology users gathered in Kinepolis Antwerp for this year’s edition of Techorama.
Secure SSH access with 2-step authentication (extended)
In this quick tutorial I’ll show you how to secure SSH access to your Linux server with 2-step authentication. Why did I call this post ’extended’? Because I’ll show you how to add extra rules so you don’t have to use 2-step authentication from certain locations. I’m not going to explain what 2-step authentication is . You’ll need SSH or CLI access to your Linux device with root rights and a 2-step authentication app on your phone, tablet or PC: